This is my personal blog, act mainly as repository of my stuffs.
A lots of content it’s written in italian, sorry.
Active projects
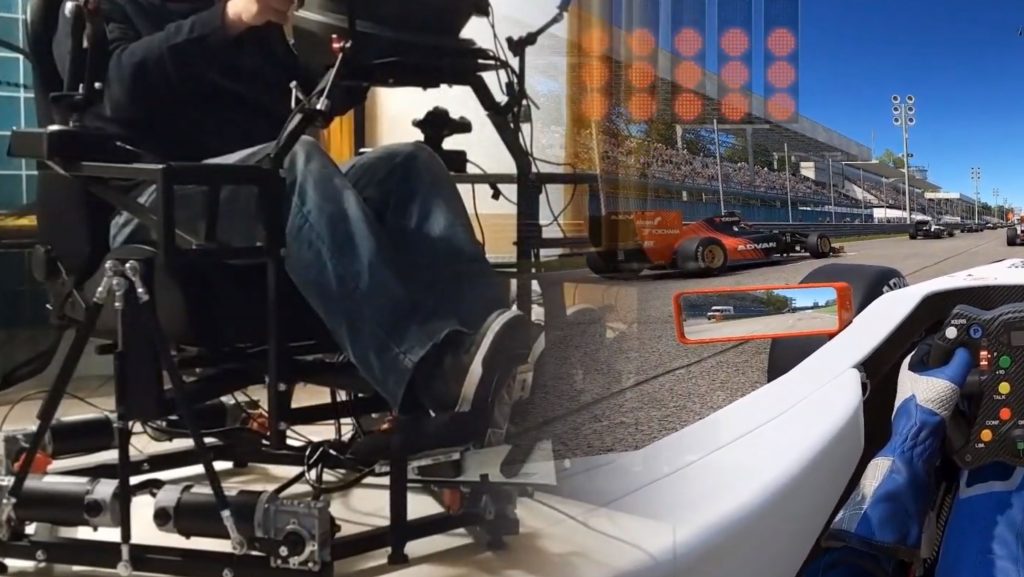
My Holodeck v2022
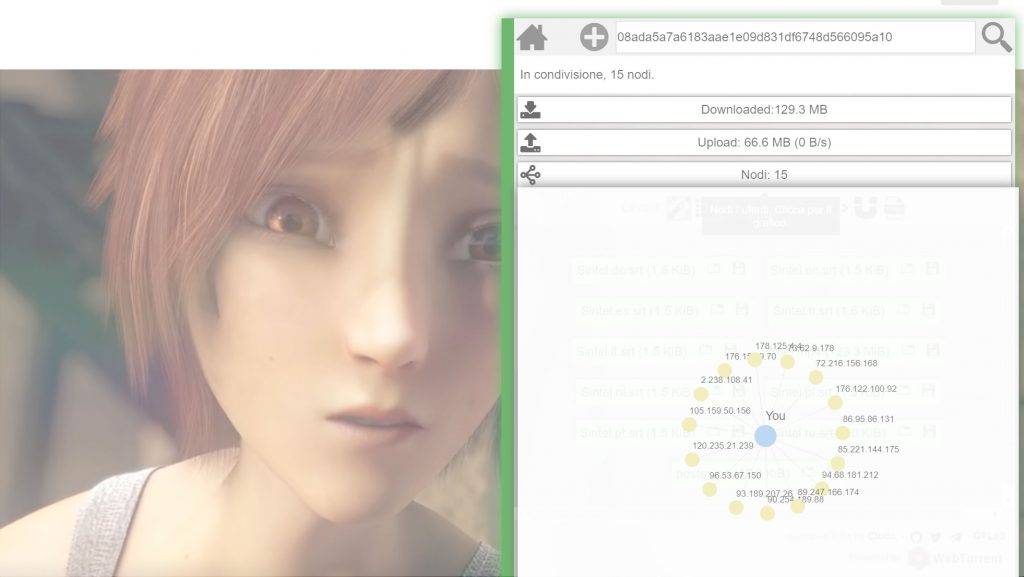
Search-ID.org
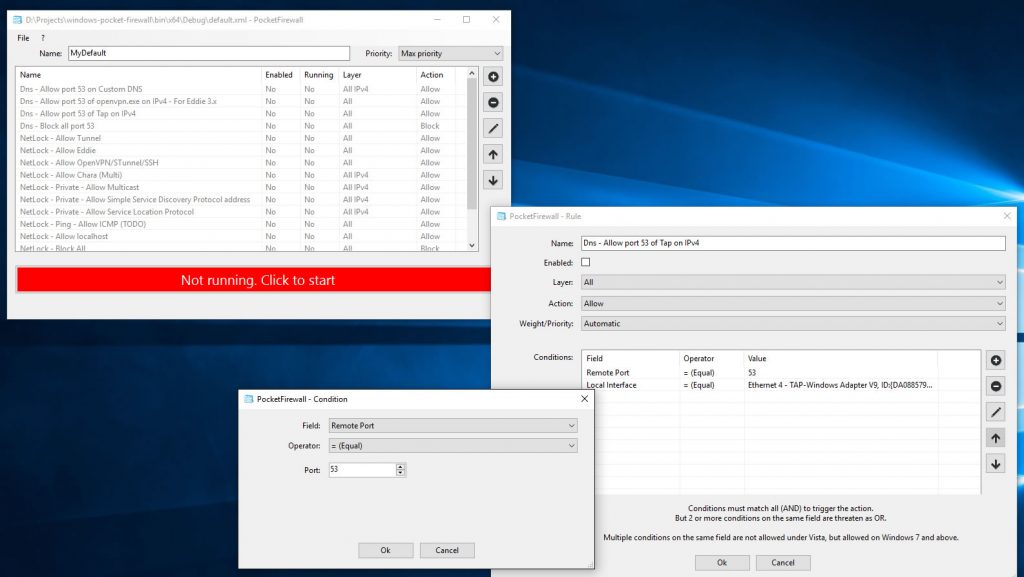
Pocket Firewall for Windows
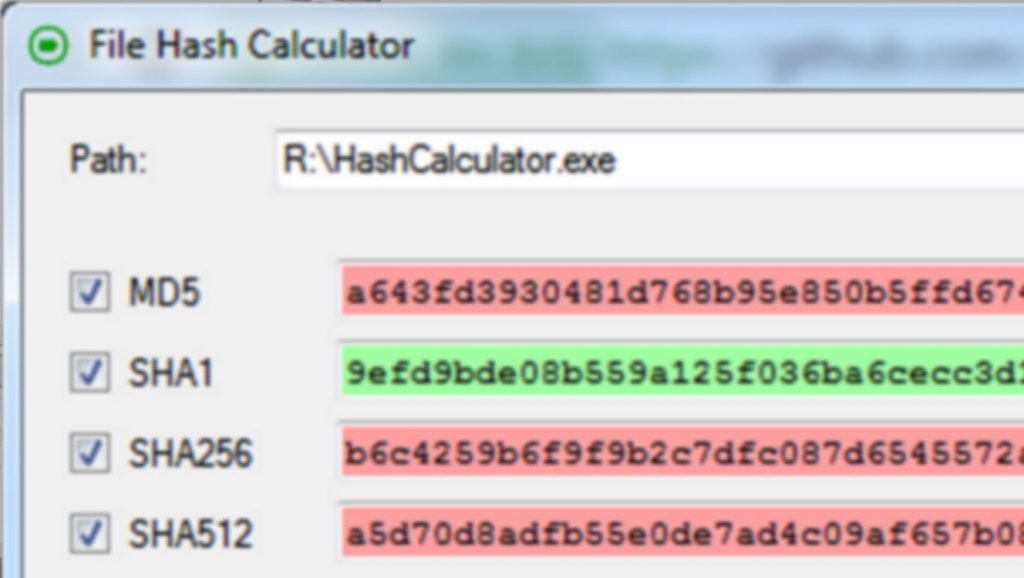
hash-calculator
Eddie – OpenVPN UI – AirVPN Client
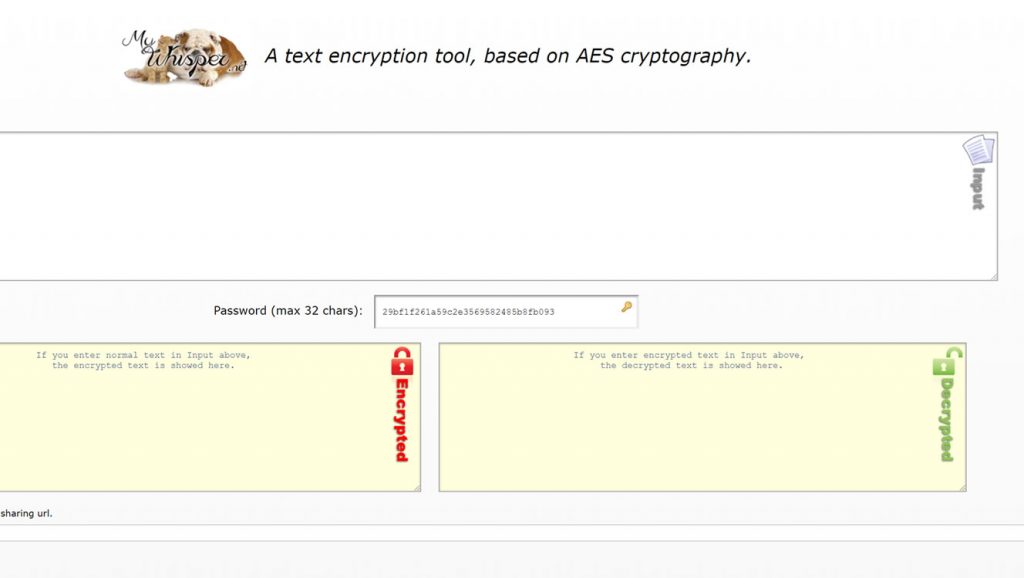
mywhisper.net
Bebras Italy
ipleak.net
Old projects
3D Vis – Indie Art – Game playground – Twitter Trends
VrSpaceTunnel
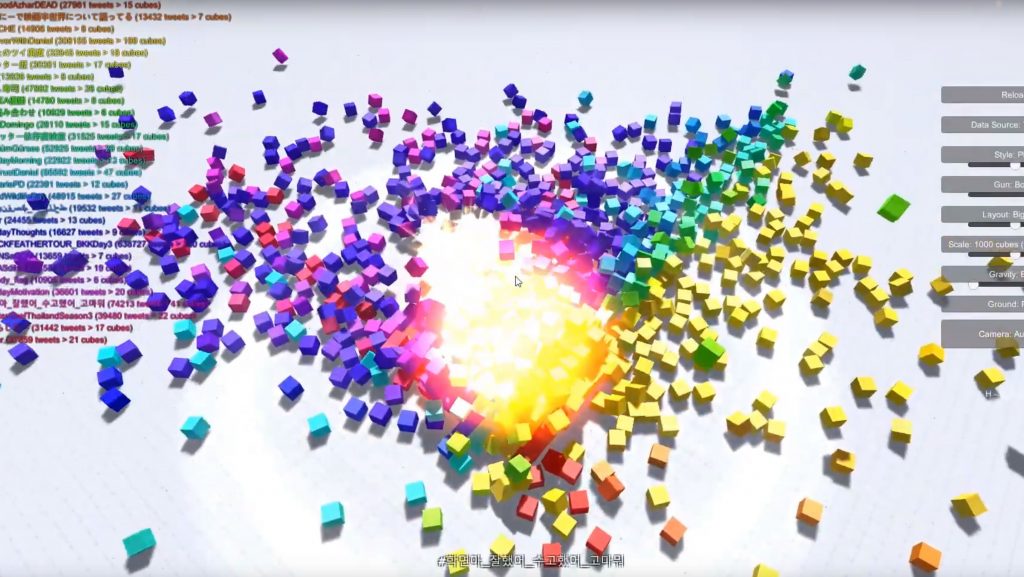
VR Fireworks
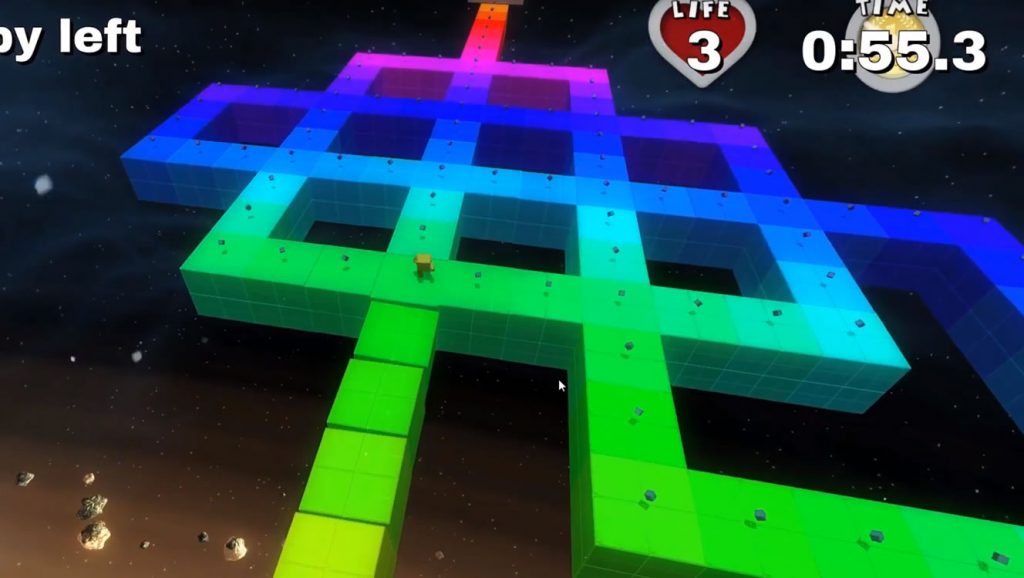
[ITA] Untitled 3D Platform game
Net Neutrality Monitor
Osiris – Serverless Portal System
Articles or works
Mastodon instance in house
3D Vis – Indie Art – Game playground – Twitter Trends
Sample ODS video
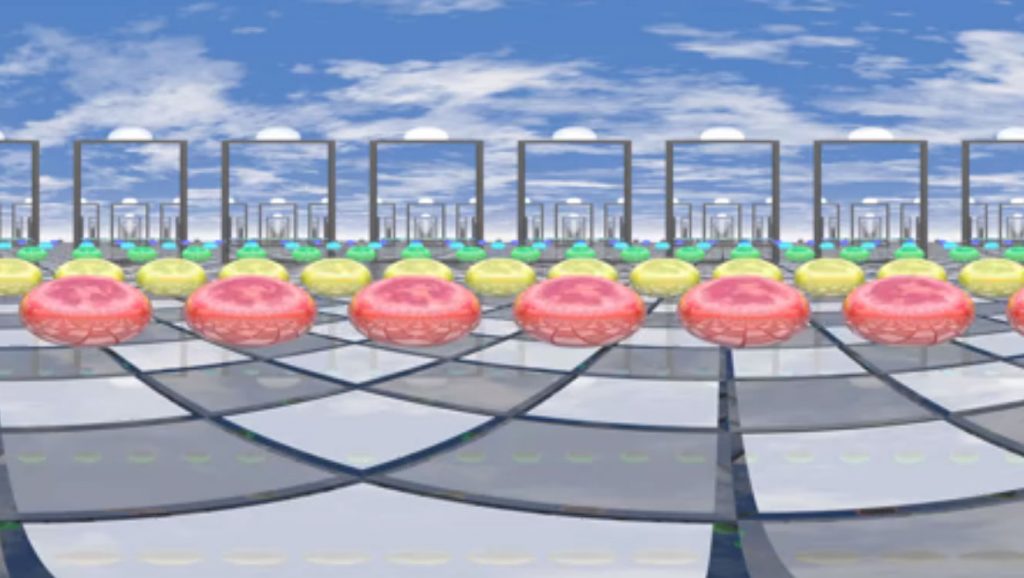
Omnidirectional stereo (ODS) with POV-Ray
VR Fireworks
AMV – Party For Two – Aion
Povray Render – Sphere spirals, 1958, MC Escher
Povray Render – Mirrors
AMV – Forsaken
All posts